The Internet of Things (IoT) has revolutionized the way we live and work. With the increasing number of connected devices, systems, and services, the IoT has become an integral part of our daily lives. However, this increased connectivity also brings increased security risks. Cybersecurity attacks on IoT devices can result in the loss of sensitive data, financial losses, and even physical harm. Therefore, it is crucial to have a monitoring system in place to discover abnormal behaviours related to cybersecurity attacks.
To address this need, we propose the Runtime Monitoring System (RMS). RMS is a monitoring system designed specifically for the IoT environment. Its primary functionalities are security monitoring and abnormal behaviour discovery. RMS is based on monitoring, analysis, and action workflows, which allows for the effective and integrated monitoring of the various devices, systems, and services that make up an IoT system.
RMS is designed to monitor IoT devices and systems at runtime, which means that it can detect abnormal behaviours and security threats in real time. This is important because most IoT devices and systems are always on and connected, so the ability to detect security threats in real time is crucial. RMS uses a variety of monitoring techniques such as network traffic analysis, system logs analysis, and behavioural analysis to detect abnormal behaviours.
More specifically, RMS is a Data collection framework which provides the specifications and relevant implementation to enable a real-time data collection, transformation, filtering, and management service to facilitate data consumers (i.e., analytics algorithms like attack detection providing real time or historical data and other third party applications for reporting abnormal behaviour). The framework can be applied in IoT environments supporting solutions in various domains (e.g., Industrial, Cybersecurity, etc.). For example, the solution may be used to collect security-related data (e.g., network, system, solution proprietary, etch.) from monitored IoT systems and store them to detect patterns of abnormal behaviour by applying simple (i.e., filtering and pre-processing) mechanisms. The design of the framework is driven by configurability, extensibility, dynamic setup, and stream handling capabilities. One of the key features of the framework is that it is detached from the underlying infrastructure by employing a specialized data model for modelling the solution’s Data Sources, Processors and Results which facilitates the data interoperability discoverability and configurability of the offered solution.
The system features lightweight monitoring probs that can be used for the data collection and publishing to the monitoring platform. The RMS provides appropriate configuration and management mechanism over the monitoring probes as well as appropriate data models and data transformation engines that enable the discoverability and reusability of the collected data. The figure below illustrates a functional diagram of the main system components.
The core system runs on the cloud as a service and connects with the Kaspersky (KSS) gateway to confirm the validity and trustworthiness of the deployed probes that deliver monitored data to it. The RMS differentiates from the KSS gateway abnormal behaviour detection on the fact that it is capable of monitoring user data except for the network data that the KSS gateway monitors. The high-level KSS gateway integration is also depicted in the Figure below.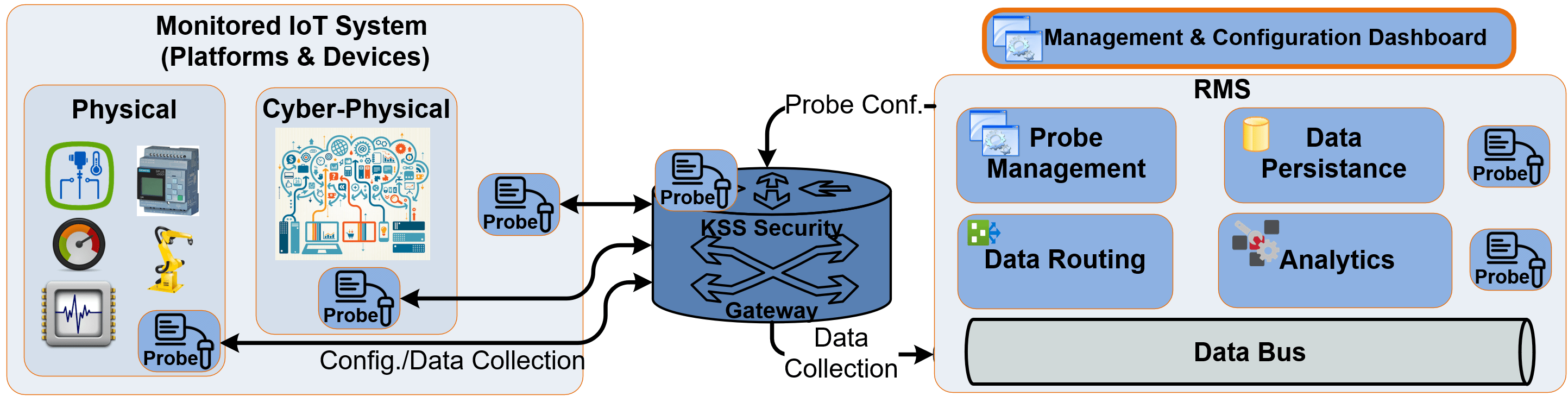
Figure: RMS high-level overview
The Figure below provides a collective Data Flow diagram of the RMS implementation which includes the primitive function of the Data Processing Engine (DPE). The DPE provides a wrapper for data processing instances (such as an algorithm or a data persistence service) that allows them to be managed and data compatible (input/output) with the Runtime Monitoring System. The RMS data models like, Processor Definition (an entity containing the characteristics of a processor such as description, vendor, availability, supported attributes, and so on), Processor Manifest (an entity containing the instantiation of a processor based on the processor description), and Processor Orchestrator (an entity containing a list of processor manifests capable of describing a complex processing flow) are all used by Processing Engine.
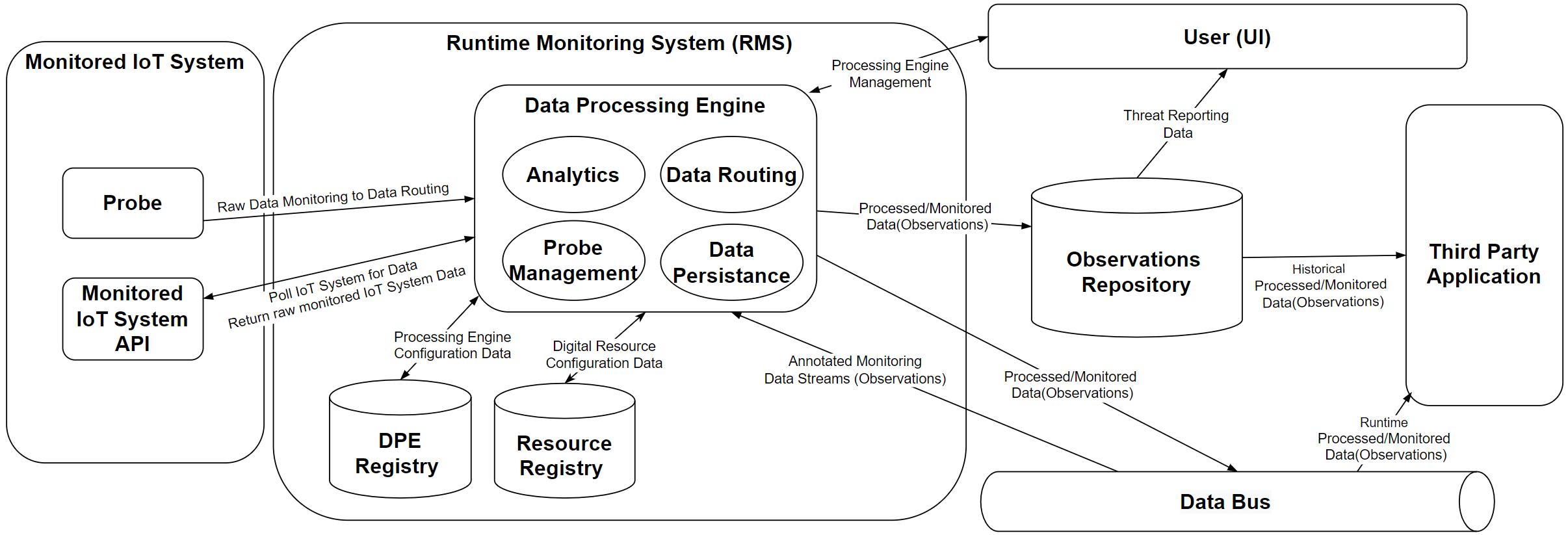
Figure: RMS Implementation Data Flow Diagram
For the IoTAC implementation RMS supports core functionalities based on the pilot requirements. The main functionalities implemented are:
- Data Routing: The component enables the transformation, annotation, and routing of incoming data streams from data probes, HTTP polling and Data Bus to various outputs. The messages are transformed to Observations using the Threat Reporting structure.
- Data Filtering: The component enables the filtering of incoming data streams based on the user (threat reporting) requirements.
- Data Persistence: The component enables the persistence of incoming messages to temporary (i.e., Data Bus) or permanent (i.e., Observation repository) data storages.
Threat Report visualization: The component enables the visualisation of captured Threat Reports providing charts, graphs, and data discovery for creating custom dashboards for the IoTAC pilots.
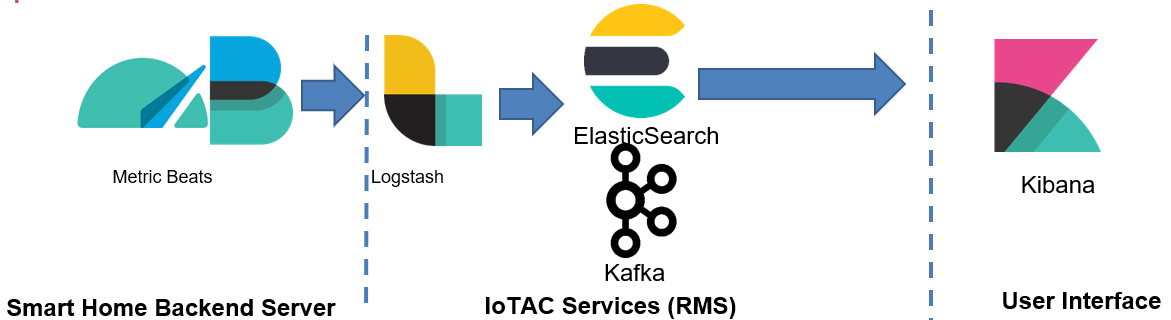
For RMS Data Collection and Processing implementation the core elements utilized for the infrastructure are Apache Kafka[1] and Elastic Stack[2] with the following roles:
- MetricBeats: to collect monitored data (i.e. CPU utilization data) by using Elastic MetricBeats deployed to the Smart Home Backend Server.
- Logstash: Raw monitored Data are transformed and filtered to match the used Data Model (i.e., Observations) and identified rules (i.e., report only values above 80%)
- Kafka & ElasticSearch: the collected pre-processed data are published to the Data Bus (Kafka) in order to be accessed by the Security Policies Manager & ElasticSearch for permeate persistence, visualization and monitoring.
- Kibana: for persisted data visualization
Figure: Elastic Infrastructure flow (Smart Home Example)
In conclusion, the Runtime Monitoring System (RMS) is a highly effective and integrated system that can be used to monitor the various devices, systems, and services that make up an IoT system. By using monitoring, analysis, and action workflows, RMS can identify, assess, and potential security threats in real time. This makes RMS a foundation for securing IoT systems and ensuring the safety and security of the data and systems that make up the IoT. RMS is partially reusing and extends existent designs and implementations from a relative system offered in the context of H2020 SecureIoT project [1].
[1] https://kafka.apache.org/
[2] https://www.elastic.co/elastic-stack/
References:
[1] Aikaterini Roukounaki, Sofoklis Efremidis, John Soldatos, Jürgen Neises, Thomas Walloschke, Nikos Kefalakis: Scalable and Configurable End-to-End Collection and Analysis of IoT Security Data: Towards End-to-End Security in IoT Systems. GIoTS 2019: 1-6