Connected Cars, and especially cooperative connected and automated mobility, are very important for the future of transportation. They can improve traffic efficiency, reduce emissions, enhance road safety, and provide better mobility services for users.
TECNALIA has set up a pilot to enable the platforms’ connectivity so as to provide a cooperative maneuver of platooning, which is dependent on communication systems for its tight control of inter-distance between vehicles. The pilot includes the Twizy vehicle platforms, which have connectivity and automated capabilities, and a control station as infrastructure, which monitors and provides high-level control to the cooperative maneuvers.
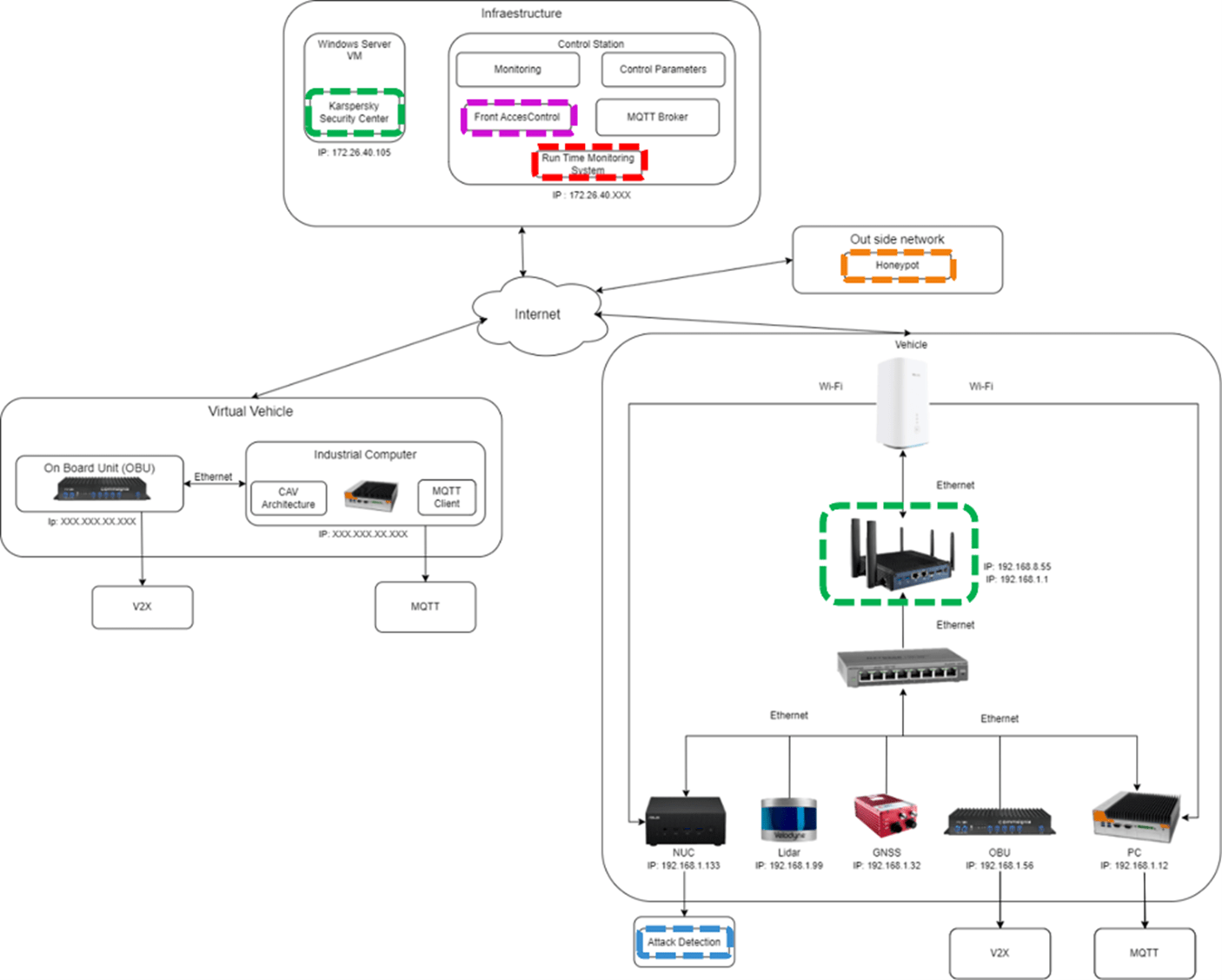
Figure 1 IoTAC platform in the Connected Car pilot
Cybersecurity remains a concern for these connected systems, which could hamper or even impede the correct functioning of the vehicle systems. TECNALIA’s automated vehicles make use of V2V communications for the platooning use cases, as well as internet connectivity via 4G. In the context of the connected car pilot, the IoTAC modules have been placed both (1) in the control station infrastructure, which will handle the platooning, to provide appropriate coverage for threats in the platooning service and (2) in the automated vehicle itself.
To this extent, the development and deployment being done in the IoTAC project referred to as this pilot, can be split into the following:
- Control station security, where one of the main concerns is the security of the information being exchanged with the vehicles’ platforms. A second concern is the availability of the platform itself and its potential exposure to attacks, which could render the service availability.
- Automated Vehicle Platform security, which tackles the possibility of attacks in the vehicle network itself, either by having a physical entry point or by exposure to internet connectivity. A second concern is the correctness of the data reported by the vehicle, and the appropriate functioning of the platform.
To this end, the IoTAC project serves as a testing ground for connected vehicle cybersecurity, by fully integrating the designed platform to tackle these concerns. The modules have been placed in accordance with the aforementioned risks, both in the vehicle and infrastructure for the control station.
The development of a monitoring framework in the IoTAC project – by aggregating different modules thus maximizing coverage – is critical to the connected car pilot. The Attack Detection module and the Security Gateway have been placed in the vehicle, monitoring all traffic data exchanged between sensors, computational equipment, and communication devices, which allows an assessment of the network state. The Honeypot module has been put adjacent to the control station, protecting it from possible malicious intruders and informing directly to a centralized IoTAC framework via a data bus.
The Front-end Access Management (FEAM) module is deployed to target the control station, specifically the authentication layer and role assignment. This module introduces a secure registration process as well as adds an additional layer of security over IoT connectivity by assigning specific roles to each user. This removes the concern regarding unauthorized access to the control station capabilities as well as manages the specific functionalities given to each role in the administration of the platoon.
A Runtime Monitoring System (RMS) is also deployed and connected via the data bus which inspects messages from the vehicle platform, the FEAM, and the Honeypot modules. From the vehicle data, it checks its correct deployment (i.e. kinematic variables within range, vehicles in the correct area, etc) and provides information via a dashboard solution. In the case of the FEAM and the Honeypot, specific messages are also shared for monitoring purposes to assess in real-time via a dashboard the correct functioning of the system.
The lessons learned from the assessment results of these IoTAC modules deployed in the connected car demonstrator will follow at the end of the project.





